.net core 3.1 Identity Server4 (添加HTTPS证书) 电脑版发表于:2021/1/7 10:59  >#.net core 3.1 Identity Server4 (添加HTTPS证书) [TOC]  通过Powershell生成X509Certificate2证书 ------------ tn>首先找到`IdentityServer4`授权服务器的工作目录下,并打开`Powershell`脚本执行如下命令 ```bash # 创建自签名证书 $cert = New-SelfSignedCertificate -Subject "CN=证书名称" -CertStoreLocation cert:\CurrentUser\My -Provider "Microsoft Strong Cryptographic Provider" ``` 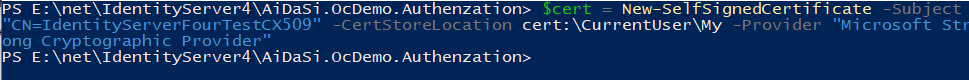 ```bash # 查看所有证书 Get-ChildItem -Path cert:\CurrentUser\My # 我这里由于证书太多了我就只看我生成的 Get-ChildItem -Path cert:\CurrentUser\My | Where-Object {$_.Subject.Contains("Id")} ``` 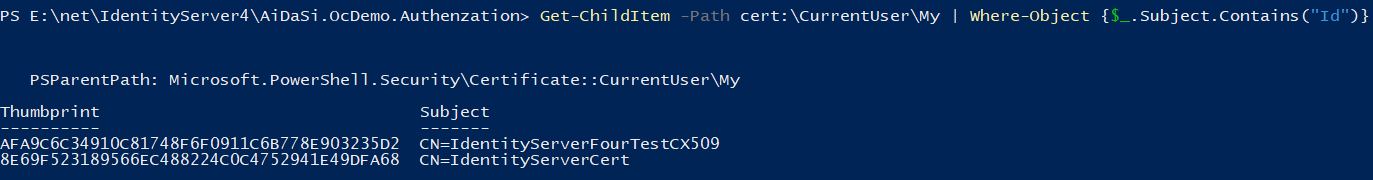 ```bash # 导出私钥 (我这里是按照我的证书导出的请你注意一下) $cert = Get-ChildItem -Path cert:\CurrentUser\My | Where-Object {$_.Subject -eq "CN=IdentityServerFourTestCX509"} # 这里是需要输入自定义用户与密码的 $cred = Get-Credential Export-PfxCertificate -Cert $cert -Password $cred.Password -FilePath "./my_cert.pfx" ```  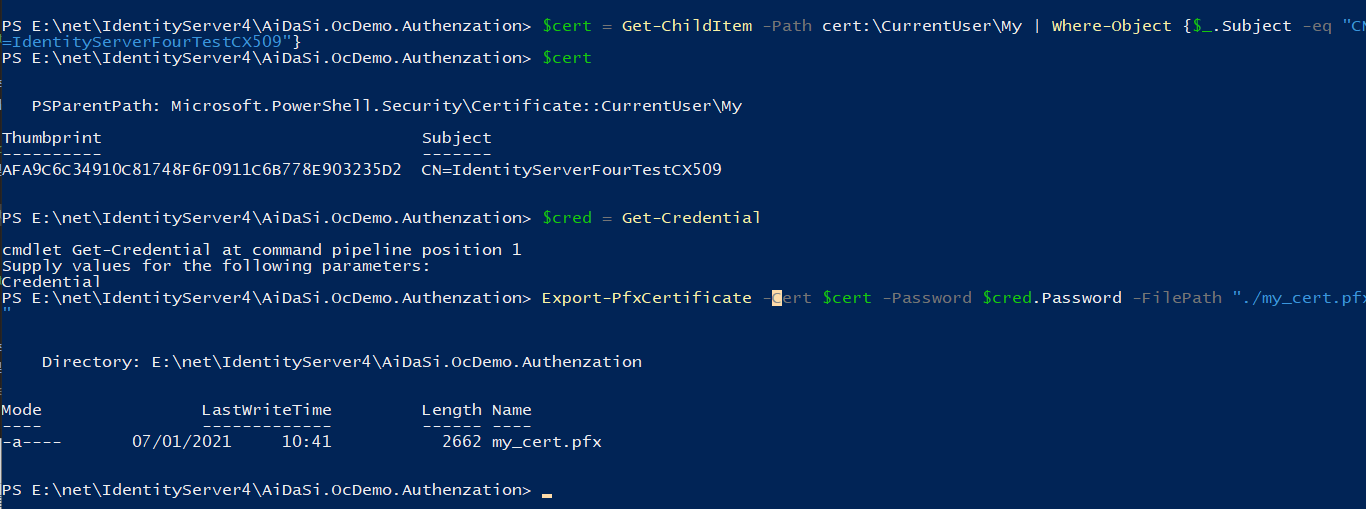  ```bash # 如果你要删除证书直接 Remove-Item -Path ("cert:\CurrentUser\My\你的证书ID") ``` 修改IdentityServer4 ------------ tn>在`Startup`类中我们进行如下修改,注意如果你的证书密码不对启动时就会报错! 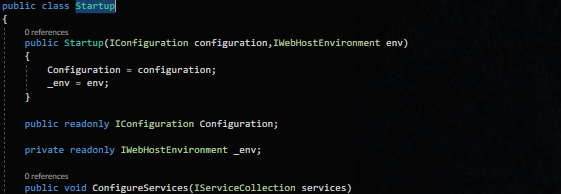 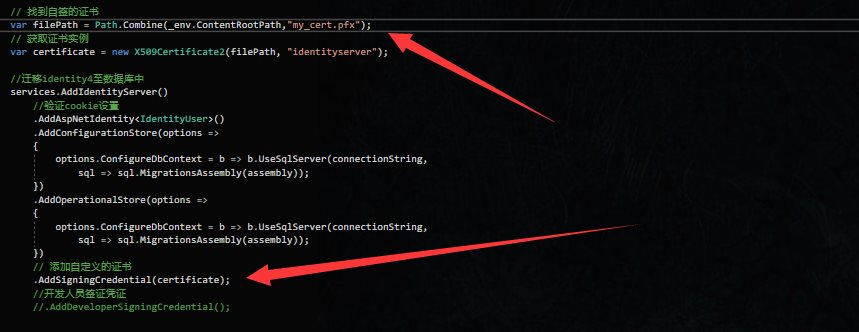 tn>测试运行,我们发现没有任何问题。 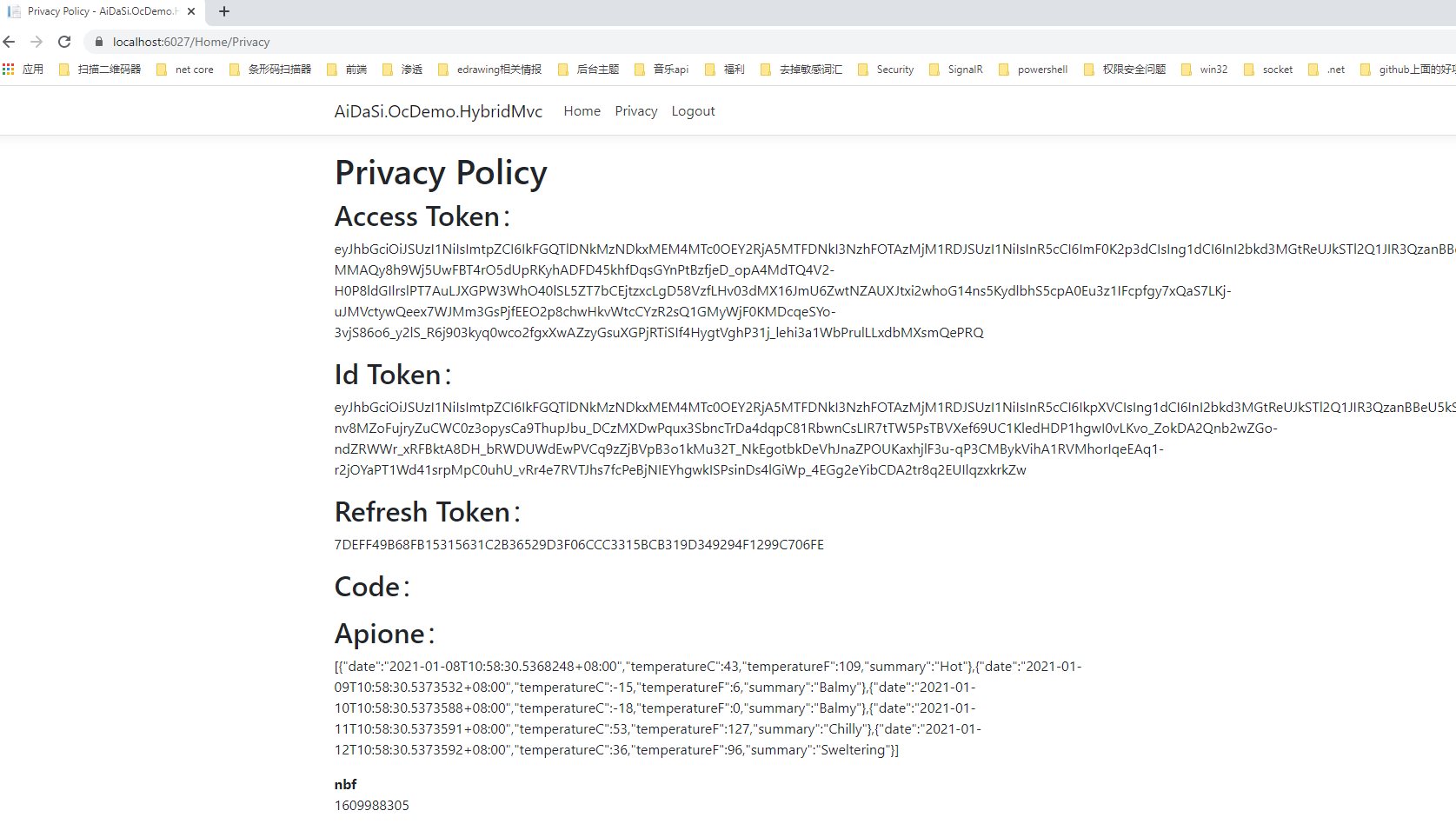 在API请求中可以做如下配置 ------------ ```csharp static HttpClientHandler GetHandler() { // var cert = new X509Certificate2(certPath, password, X509KeyStorageFlags.MachineKeySet | X509KeyStorageFlags.PersistKeySet | X509KeyStorageFlags.Exportable); var handler = new HttpClientHandler(); handler.ClientCertificateOptions = ClientCertificateOption.Manual; handler.SslProtocols = (SslProtocols.Tls | SslProtocols.Tls11 | SslProtocols.Tls12 | SslProtocols.Ssl3); handler.ServerCertificateCustomValidationCallback = (sender, cert, chain, sslPolicyErrors) => true; return handler; } services.Configure<IdentityModelConfig>(configuration.GetSection("Identity_Config")); // Microsoft.IdentityModel.Logging //IdentityModelEventSource.ShowPII = true; services .AddAuthentication("Bearer") .AddJwtBearer("Bearer", config => { config.Authority = configuration.GetSection("Identity_Config:Authority").Value; // 授权服务器地址 //确定自己是哪个资源(资源名称) config.Audience = configuration.GetSection("Identity_Config:Audience").Value; bool.TryParse(configuration.GetSection("Identity_Config:IsHttps").Value,out var _IsHttps); bool.TryParse(configuration.GetSection("Identity_Config:ValidateIssuer").Value, out var _ValidateIssuer); bool.TryParse(configuration.GetSection("Identity_Config:ValidateAudience").Value, out var _ValidateAudience); // 解决证书问题 config.BackchannelHttpHandler = GetHandler(); config.RequireHttpsMetadata = _IsHttps; // 是否使用https进行通信 //取消验证用户以及验证角色 config.TokenValidationParameters = new Microsoft.IdentityModel.Tokens.TokenValidationParameters() { ValidateIssuer = _ValidateIssuer, ValidateAudience = _ValidateAudience, //每间隔1分钟去检查Token是否有效 ClockSkew = TimeSpan.FromMinutes(30), //要求运行有超时时间 RequireExpirationTime = true, }; ```